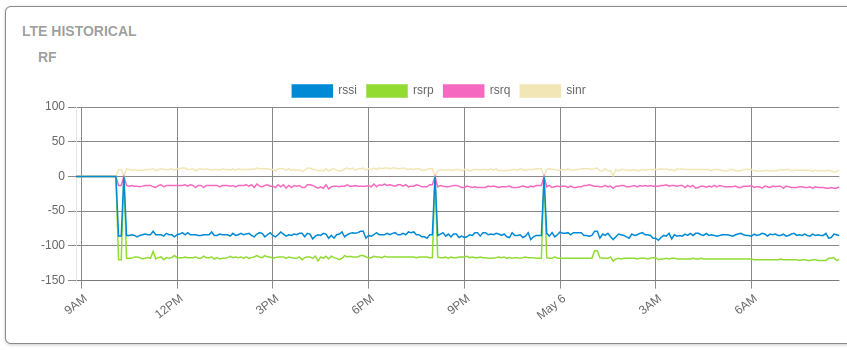
Recently we helped a new Admiral customer onboard a MikroTik that is configured to send…

Security best practices, part 2.
Welcome to part 2 of our security best practices series. In this article we’ll go over usernames and passwords and Virtual Private Networking. In case you missed part 1, find it here:
Usernames and Passwords
You’ve probably heard it a million times – use strong passwords. Letters, numbers, mixed case, symbols, and lots of characters. If you need a visual for why it’s important, check here for a nice graphic of how long it takes a hacker to brute force a password: https://www.hivesystems.io/blog/are-your-passwords-in-the-green Ultimately, if a bad guy can guess or crack your password, they can get access to lots of your stuff.

Hopefully, you understand why that’s important, so let’s discuss some of the things that aren’t always part of the conversation, like not reusing passwords. Why does that matter? Well, if you use the same login info, username and password, for several accounts, then if any single one of them becomes compromised they can all be compromised.
For example, if someone gets into a social media account, and it’s the same info as your email, they now have your email. If that same login is used for banking, they now have access to not only your bank info but potentially a second factor of authentication with your email. The same holds true for server and router logins. Don’t use the same password, and if you can, use different usernames.
With RWB, we use randomized usernames, randomized passwords, and different usernames and passwords for each router and user. What this means is that even if one router VPN credential is hacked, they still can’t log in because the user account is different from the VPN account – and add to that they’d have to get through our firewall filtering and ACL!
For random usernames and passwords, we like to use https://randomkeygen.com.
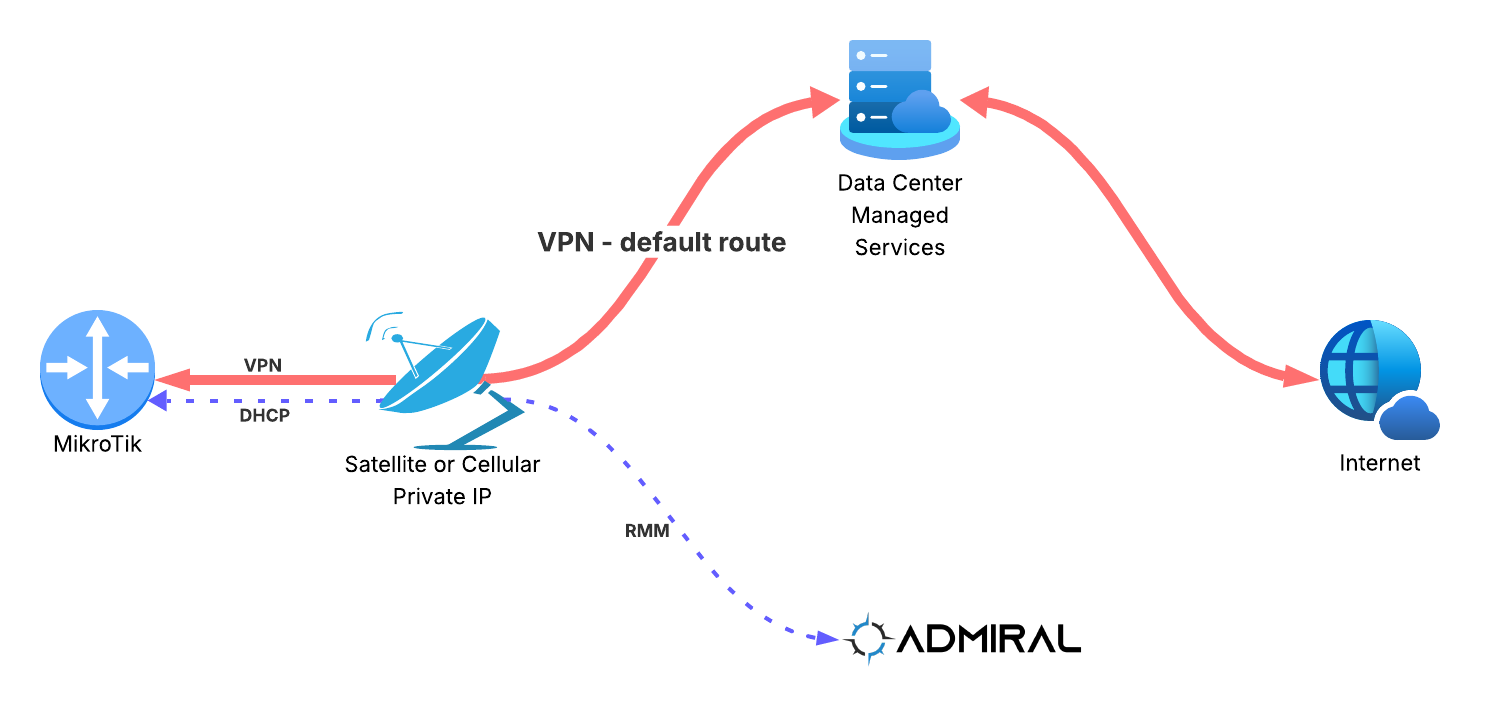
VPN and encrypting traffic
Any packet can be inspected by anyone in the traffic path. For example:
Client ←→ WiFi router ←→ Service Provider ←→ Internet ←→ Service Provider ←→ Server
In the above packet flow, which is already summarized, there are several points at which packets could be inspected, or “sniffed”. Packet sniffing is a technique where packets are captured – or copied – off the network and into an analyzer, allowing for an observer to take a look at the payload – or the insides – of packets.
With a program like Wireshark, or tcpdump, etc. anyone on the WiFi network, or with access to the Service Provider gear, or several of the abbreviated locations included in that big cloud we call the Internet, could monitor and promiscuously watch your traffic – or more accurately look at the streams and flows created by your Client!
Many applications do a good job at creating what’s called end-to-end encryption, where the client and server do a handshake and agree on a strategy to keep a conversation private from prying eyes. But, do all applications encrypt the packet stream? Hardly.
So what can you do to protect your data streams from casual observers? You can use a VPN, or virtual private network. With a VPN, the traffic at both the endpoints of the tunnel agree to encrypt and unencrypt the traffic they put on and take off the network with an algorithm. There are many encryption schemes and protocols, as well as many types of VPNs that are well beyond the scope of what we’re going over today.
How does RWB leverage VPN? We create a VPN tunnel between our service and your router, allowing you to send and receive traffic to your Tik that’s secure. From health information to backups (exports) to logging in to run remote commands – the VPN is encrypting and protecting that traffic.