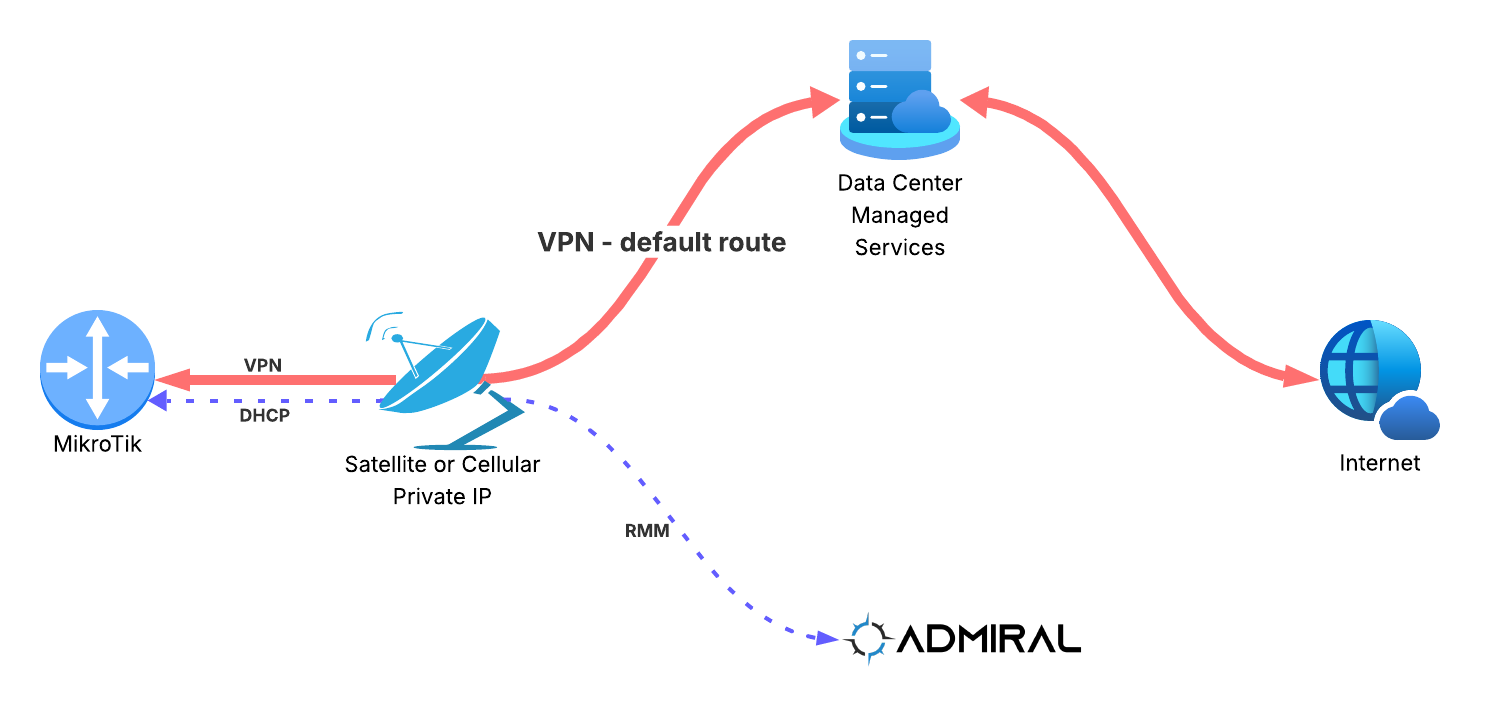
Recently we helped a new Admiral customer onboard a MikroTik that is configured to send…
How RemoteWinBox & Team Cymru are Making the Internet a Safer and More Secure Place
What’s the problem?
Cybercriminals will make use of every trick in the book to accomplish their goals. When the bad guys want to do bad things on computer networks, they have to send data over the network.
Often times in order to avoid detection and improve their chances of delivering the payload of bad stuff like malware, viruses or other nefarious intent like hacking or exploiting, they’ll use IP addresses that aren’t considered real. Addresses that aren’t real are called BOGONS.
How can an IP address not be real, but also be real enough for an attacker to use, you might be wondering. In all of IPv4, the range of IP addresses is from 0.0.0.0 through 255.255.255.255, so by default all the routers that run the Internet will forward and process any traffic within that range.
But, there are a few scenarios where IP addresses, also called prefixes or subnets, within that range are actually invalid, illegitimate, or non-routable:
- The IP’s are designated as private and should never be routed across public networks, like the Internet
- The IP’s are designated as reserved and should not be routed
- The IP’s are routable and legitimate, but have not yet been assigned by a numbering authority and are unused so should not be routed (yet)
In addition, here’s what Team Cymru has to say:
From the website: https://www.team-cymru.com/bogon-networks :
What Is a Bogon, and Why Should I Filter It?
A BOGON prefix is a route that should never appear in the Internet routing table. A packet routed over the public Internet (not including over VPNs or other tunnels) should never have an address in a BOGON range. These are commonly found as the source addresses of DDoS attacks.
BOGONS
Bogons are defined as Martians (private and reserved addresses defined by RFC 1918, RFC 5735, and RFC 6598) and netblocks that have not been allocated to a regional internet registry (RIR) by the Internet Assigned Numbers Authority.
Why you should care
ISP’s, especially WISP’s (Wireless ISP’s) have a unique problem in that they use wireless communications systems to push the packets to and from their customers. These wireless backhaul radio systems have a very finite amount of bandwidth and time available to send or receive data. If a wireless system is wasting time and bandwidth on sending useless packets, this can have a significant impact on performance and thus the Customer Experience.
If a WISP’s network is sending packets to or from IP blocks that shouldn’t be reachable, then this is a waste of valuable resources.
Said another way, you can run your network clean without Bogons, or it can be congested with BOGON traffic that shouldn’t be there.
Traditionally WISP’s have filtered at the “Head End” of their network. This works well for one side of the packet flow – packets from the internet going toward a customer. But if the ISP is also filtering packets from the customer going out to the internet at the head end, then they have paid for packets to be transported on their network only to toss them in the rubbish bin after they’ve already clogged up the pipes and traversed the backhaul network. What a waste of resources!
How can we do better??
First is to filter at BOTH the Head End *AND* at the closest point to the subscriber. This close subscriber point may be the tower the AP is connected to, or it may be a router located at the subscriber’s home or business.
Managing a list of IP’s and getting it correct and keeping it current is a hard and time-consuming process. Enter Team Cymru, a trusted partner in the ISP community. With the TC BOGON’s feed, you can be confident that the list of IP’s provided are validated and that they should not appear in the global internet. Team Cymru constantly updates this list to keep it fresh and accurate.
An ISP can use the TC Bogon’s feed to build packet filters or route filters to cause traffic to be dropped. You can implement this on your Head-End router(s) and thus prevent traffic FROM these BOGON addresses from entering your network, and you can also keep packets from leaving your network. In addition, these BOGON addresses can be placed at tower sites, customer routers, etc, and by doing so you will keep traffic from entering your network from the customer that shouldn’t be there.
How does RemoteWinBox help / fit in? – From John at Team Cymru
The next challenge is how to distribute this list to hundreds or thousands of routers across your subscriber network??
Enter RemoteWinBox!
If you are running Mikrotik routers then RemoteWinBox is the tool for you. With RemoteWinBox you can configure TC Bogons with one button press and RemoteWinBox will then automatically push out the configuration and update it automatically to all of your routers, updating once daily to keep current without the need for any human interaction. Not only are you enhancing your network, but you are also doing your socially responsible part in keeping the Internet Safe, or as we do at TC “To Save and Protect Human Lives.”
So be an Internet Hero and check out how RemoteWInBox and Team Cymru can help, and watch out for further integrations between RWB and TC as we look to continue making the internet a safer, more secure, and socially responsible world.